The Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) is a key centerpiece of the National Cybersecurity Strategy Implementation Plan.
Part of the Consolidated Appropriations Act of 2022, CIRCIA empowers the Cybersecurity and Infrastructure Security Agency (CISA) to collect and analyze reports on cyber incidents, thereby enhancing its visibility into the cyber landscape wreaking havoc on businesses around the globe.
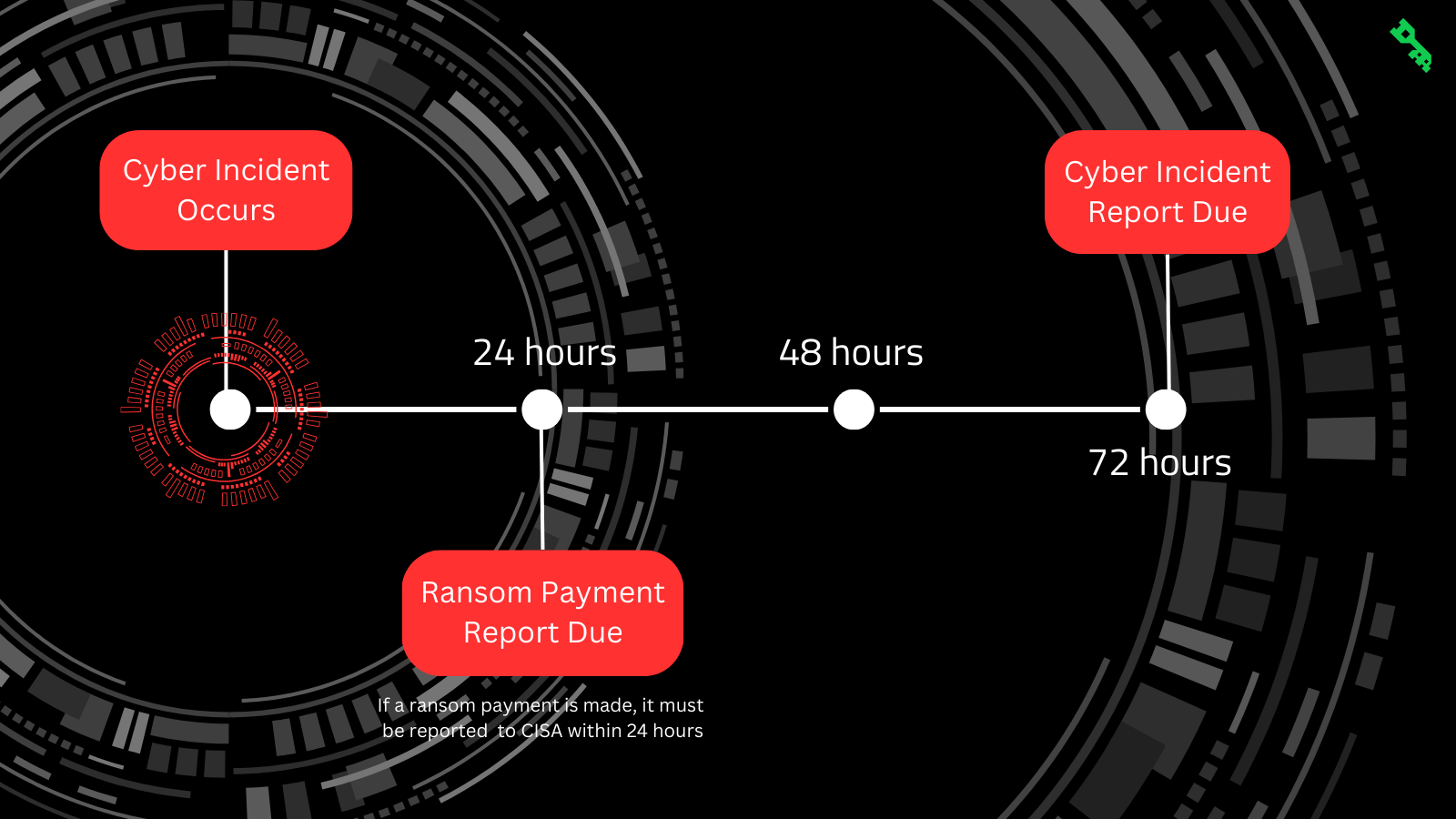
CIRCIA mandates that “covered entities” report “significant” cyber incidents within 72 hours of occurrence. If a covered entity makes a ransom payment, it must be reported within 24 hours. While the details have yet to be fully defined, the bill outlines submission requirements that are far broader than, for instance, complaints submitted to the FBI’s Internet Crime Complaint Center (“IC3”), including technical details and tactics, techniques, and procedures (“TTPs”) related to the incident.
The information reported to CISA will not be used as evidence in the context of US courts, regulatory bodies, or local government legal proceedings. All reports received from designated entities enjoy protection from the federal government to encourage robust information-sharing that may be leveraged by federal agents for cybersecurity purposes. Specifically, these purposes encompass threat identification and response, threat to minors investigations, and cyber incident prosecution.
In instances where the Director of CISA suspects a cyber incident or ransomware payment has occurred yet remains unreported, they may request additional information to confirm or deny such suspicion. In accordance with Sec. 2244, if a satisfactory response to the request is not received within 72 hours, a subpoena may be issued to compel disclosure.
Although CISA is already advocating for voluntary sharing of cyber incident information to safeguard other organizations from similar threats, the National Cybersecurity Strategy Implementation Plan suggests that rulemaking for the final CIRCIA law will not be complete until late 2025 or even into 2026.
CIRCIA signals a watershed moment in the Federal Government’s approach to cyber incident reporting. In the aftermath of Colonial Pipeline and other high-profile ransomware incidents in 2020-2021, the Biden Administration and Congress looked at a wide range of possible solutions, including banning ransomware payments, banning cyber insurance coverage for cyber extortion, and banning cryptocurrencies like Bitcoin and Monero.
None of these reactionary measures gained traction in national policymaking. Previous reporting practices, which relied mainly upon self-disclosure, yielded inadequate information. Instead, CIRCIA favors a more proactive approach, primarily aiming to increase Law Enforcement’s visibility into the scope and scale of ransomware. CISA accepts that cyber extortion is a cost of doing business in today’s world and, through CIRCIA, hopes to address it proactively.
DAR will monitor the impact of this legislation on the cybersecurity landscape from the perspectives of business owners, the general public, and those processing the reports. Adhering to these reporting requirements may pose serious challenges for organizations, particularly during the disarray of a cyber incident. As with so many other parts of effective incident response, planning and preparedness will be a necessity.
This post is part of DAR's "Federal Fridays" series. Be sure to follow DAR on LinkedIn for the latest updates!